This blog post covers a boring local privilege escalation bug in iStat Menus due to a misconfigured folder permission. I was honestly surprised this was overlooked, since there were other recently disclosed vulnerabilities, one of which was way more interesting. Read here.
TL;dr
- Insecure world-writable folder allowing privilege escalation
- Affected versions
< 7.20.5withInstall Helpercomponent - No profit (a reboot is required)
- A CVE has been requested
Description
In my day-to-day job I occasionally review software for security issues. I came across an app called iStat Menus by Bjango software. The app is basically like the Apple’s activity monitor but on steriods. It allows users to recieve notifications, monitor network usage, and much more.
During the initial install you will be asked to install the Install Helper. This is actually the vulnerable component. You will be asked to provided sudo privileges to continue. If you skip this step you won’t be affected by this bug.
Once installed a new privileged service called com.bjango.istatmenus.daemon will be present. The full path of this binrary is:
/Library/Application\ Support/iStat\ Menus\ 7/com.bjango.istatmenus.daemon
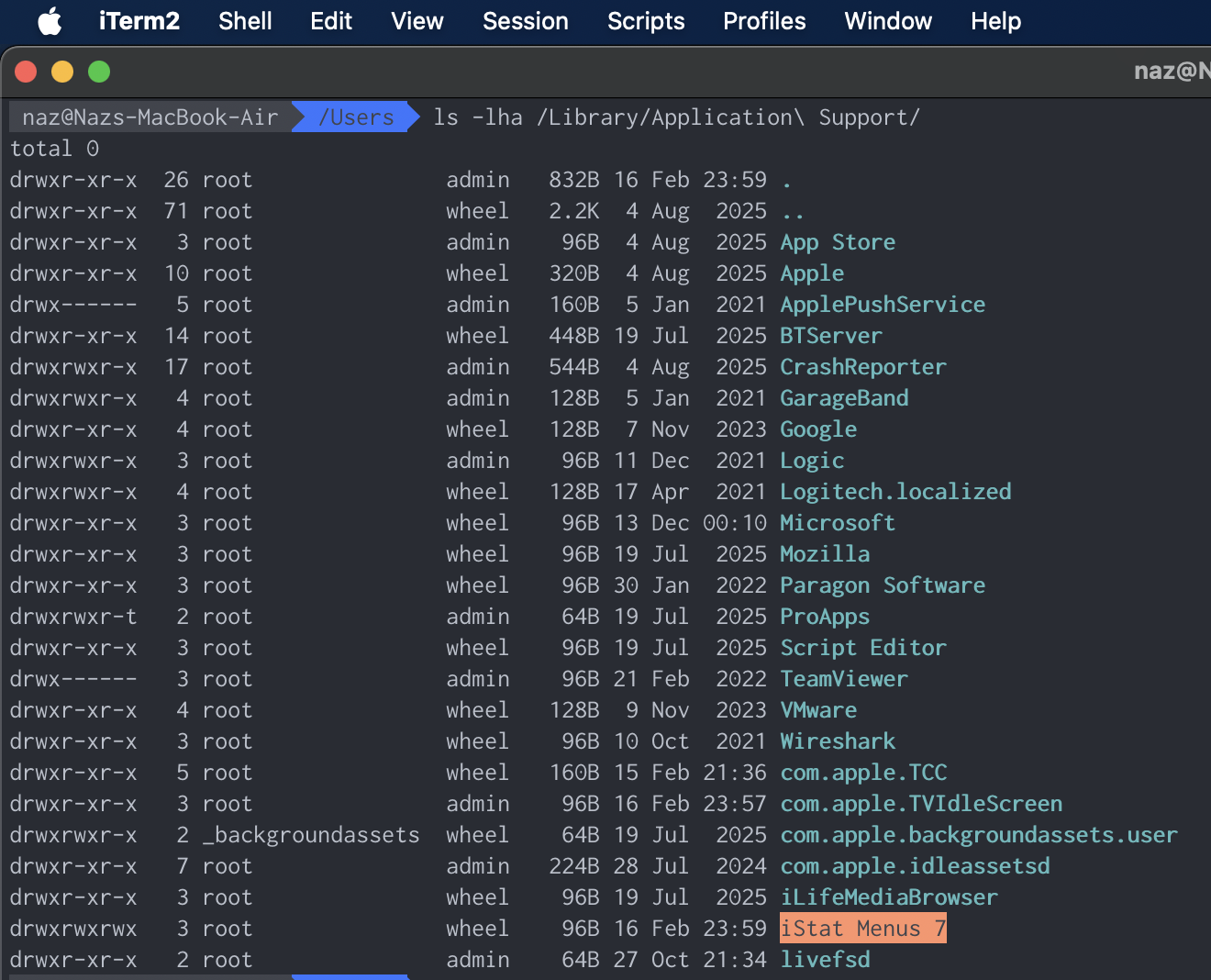
And the parent folder of this service:

Highlighted in orange, we can clearly see the permission drwxrwxrwx is set. Other users can read, write, and execute that folder. The com.bjango.istatmenus.daemon is owned by root but the upper directory is misconfigured which may lead to privilege escalation.
You could also inspect the com.bjango.istatmenus.installer.log in Console to see where the problem starts.
...
2026-02-16 23:59:51.894 com.bjango.istatmenus.installer[98143:44761071] Starting with bundle - /Applications/iStat Menus.app/Contents/Resources/Components.bundle
2026-02-16 23:59:51.894 com.bjango.istatmenus.installer[98143:44761071] /bin/mkdir /Library/Application\ Support/iStat\ Menus\ 7/
2026-02-16 23:59:51.914 com.bjango.istatmenus.installer[98143:44761071] /usr/sbin/chown -R root:wheel /Library/Application\ Support/iStat\ Menus\ 7/
2026-02-16 23:59:51.932 com.bjango.istatmenus.installer[98143:44761071] /bin/chmod -R 777 /Library/Application\ Support/iStat\ Menus\ 7/
The last line with /bin/chmod -R 777.
How to abuse this?
Easy, replace the com.bjango.istatmenus.daemon binary with a malicious one. But there is a catch, low privileged users are not able to restart this service. However, we can do a reboot which macOS system will happily restart the service.
This vulnerability is more of a concern to corporate devices with policies that restrict user sudo access, rather than home devices because most of us are running admin accounts anyway, and can quickly elevate to root.
Download
Note: The official site https://bjango.com/mac/istatmenus/ will only download the latest (patched) version. To follow along you can use the link (CDN) below. The last affected version is iStat Menus 7.20.4 (2265) and is available at:
https://cdn.istatmenus.app/files/istatmenus7/versions/iStatMenus7.20.4.zip
Uninstall
Even after you uninstall the app, there are several start-up scripts and background services that still remain. The following commands should remove all of them. I’m not sure why the default uninstaller doesn’t do this.
sudo rm -rf /Library/PrivilegedHelperTools/com.bjango.istatmenus.installer
sudo rm -rf /Library/LaunchDaemons/com.bjango.istatmenus.installer.plist
sudo rm -rf /Library/Application\ Support/iStat\ Menus\ 7
sudo launchctl remove com.bjango.istatmenus.status
sudo launchctl remove com.bjango.istatmenus.agent
sudo launchctl remove com.bjango.istatmenus.installer
Summary
This vulnerability reminded me of my OSCP course. There was a very similar challenge flag on a Windows system which allowed regular users to elevate to system by editing an insecure path that contained a binrary. But the user didn’t have permissions to restart the service. The trick was to reboot the machine and let Windows start the service for you.
Always remember to go for the low hanging fruits.