In this post I will go into technical details on what attackers could do with the stolen encrypted vaults, specifically how they could use tools like Hashcat to crack vault passwords and get access to sensitive log-in credentials.
To simulate the stolen data, I will use my test Lastpass account to extract an encrypted vault from the Chrome Browser extension on macOS. Following this, I will use a wordlist attack to bruteforce the vault which has a weak and guessiable password.
Update: Fixed a few mistakes and added more clarification.
Update 2: More clarification on cracking section, added unencrypted URLs to the what was stolen section, and added a link to a Hashcat benchmark for Lastpass from 2013.
What happened?
The Verge published an article which includes a great summary of the breach. There is also a blog post by Lastpass themselves. To summarise, in August 2022 Lastpass suffered a data breach where customer data and source code was stolen. Lastpass didn’t do a good job at letting the public (and customers) know of how bad the breach actually was.
What was stolen?
- a backup of customer vault data
- unencrypted website URLs
- company names, end-user names, billing addresses, email addresses, telephone numbers, and the IP addresses
- source-code and other intellectual property
What can attackers do with the stolen vaults?
It really depends, there are a lot of things to consider. A few things that spring to mind are:
- How are the encrypted vaults stored in the cloud?
- Did a customer set a weak and easily guessed vault password?
- What is the key iteration (default or custom)?
- Other factors not covered?
And since I don’t know what the stolen data looks like, or how it may be encrypted, this blog post is only a theory and estimation based on data I have access to. This includes the SQLite database used by the Browser extension and data within it.
In the next sections I will demostrate how to extract the encrypted vault database from the Chrome extension and pull out specific information to start cracking with Hashcat.
Lastpass Browser extension
On Chrome Browsers each extension has a unique ID. The Lastpass extension uses hdokiejnpimakedhajhdlcegeplioahd as the ID. You can confirm this by visiting the URL chrome-extension://hdokiejnpimakedhajhdlcegeplioahd/vault.html in your address bar. You will be presented with the vault log-in page.
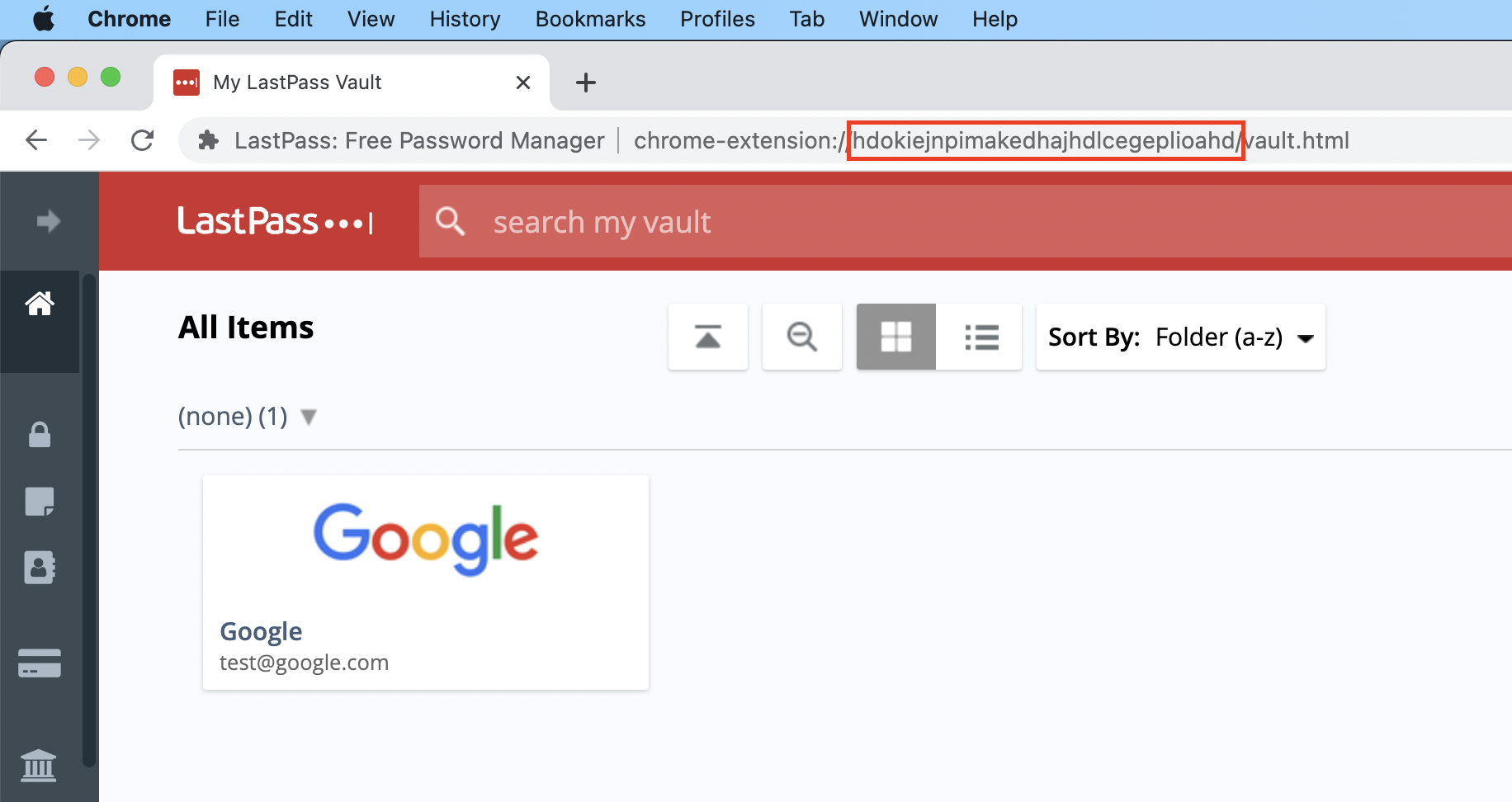
You can think of it as a local site that uses HTML and JavaScript within your Browser.
Extracting encrypted vault
All extensions have their own folders which are stored locally on the system in various locations depending on OS.
As per online documentation the Lastpass support page states devices using Chrome Browsers on Windows systems store the vault data in the following PATH:
%LocalAppData%\Google\Chrome\User Data\Default\databases\chrome-extension_hdokiejnpimakedhajhdlcegeplioahd_0
On macOS systems the location is slightly different:
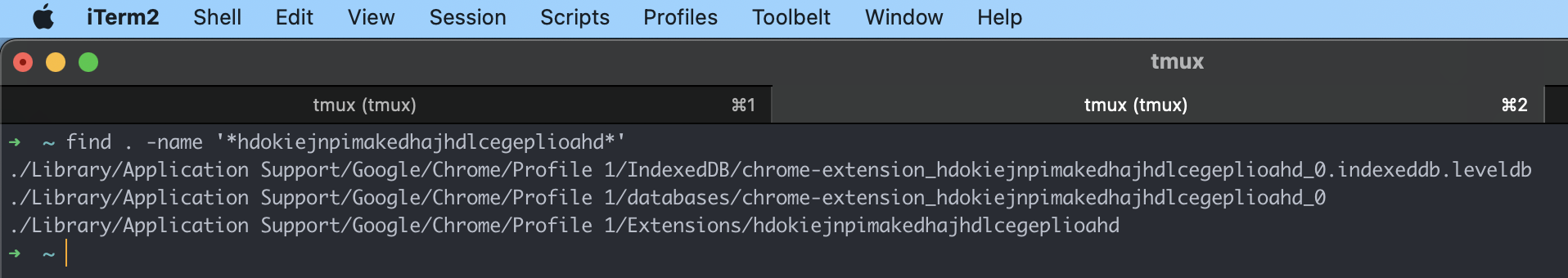
Note: I use two Profiles on Chrome, hence why you see Profile 1 instead of Default.
Lastpass SQLite database
In this folder a SQLite file named 1 with the version: SQLite version 3039004 should be present. This is where encrypted vault data is stored and used by the extension.
➜ file 1
1: SQLite 3.x database, last written using SQLite version 3039004, file counter 21, database pages 22, cookie 0x5, schema 4, largest root page 11, UTF-8, vacuum mode 1, version-valid-for 21
You can then use a tool like DB Browser for SQLite to view the database contents. I also copied it to Desktop and renamed the file to lastpass-vault-macos-chrome.sqlite so it’s easier to remember.
All the interesting data is stored in a table called LastPassData.
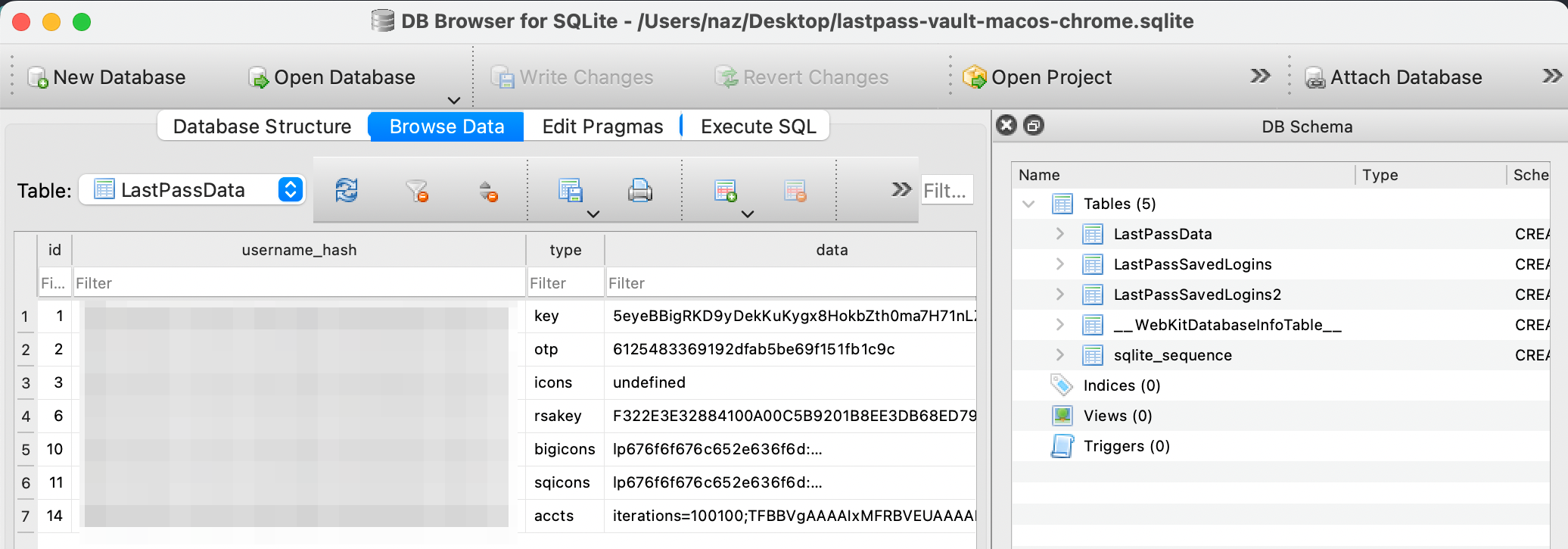
To start cracking Lastpass vault passwords using Hashcat you need three things:
- Key value
- Iteration count
- Account email address (hashed in database)
These need be formatted like so: KEY:ITERATION:EMAIL
Key value
To retrieve the key value, search column type where value key, and then in the data column select the second row e.g. T4vInfZ+6MGDeEendq4gvA== as shown below:
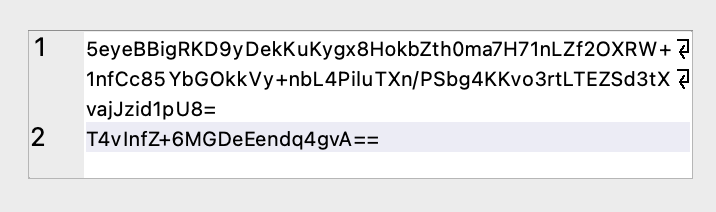
You can also execute the following SQL query:
SELECT substr(data, -24) FROM LastPassData WHERE type = 'key';
It is base64 encoded, which you can decode and get the hex value by:
echo "T4vInfZ+6MGDeEendq4gvA==" | base64 -d | xxd -p
We now have the first requirement: 4f8bc89df67ee8c1837847a776ae20bc
Iteration count
To retireve the Iteration count, search column type where value accts, and then in the data column the first few charaters before the ;. Lastpass changed the default iteration in 2018 from 5000 to 100100.
You can also execute the following SQL query:
SELECT SUBSTR(data,0,INSTR(data,';')) FROM LastPassData WHERE type = 'accts';
We also now have the second requirement: 100100
The database contains a hashed email address value. But we do know that attackers already have this info since the recent Lastpass compromise included email addresses. For the purposes of this blog, I am not going to share the email address which I used.
Formatted hash
With all the requirements the hash should look like this:
4f8bc89df67ee8c1837847a776ae20bc:100100:[email protected]
Cracking Lastpass vaults with Hashcat
As a proof of concept I used my MacBook Air with the M1 chip to crack passwords. The speed was absolutely horrible 1110 H/s (hashes per second), but it did work. Attackers on the other hand can leverage multi-GPU device setups with optimised drivers that could easily reach speeds of 2,000,000+ H/s e.g. a benchmark from 2013.
As an example of bruteforcing vaults with weak passwords, I downloaded the popular rockyou.txt wordlist and put my actual vault master plaintext password inside (I was lazy and didn’t want to reset my password to a weak one), obiviously attackers can’t do this.
I then set the following Hashcat options:
hashcat -a 0 -m 6800 lastpass-hash.txt ~/Downloads/rockyou.txt
-a 0attack mode Wordlist-m 6800Lastpass hash algorithmlastpass-hash.txthash formatted (KEY:ITERATION:EMAIL)rockyou.txtwordlist of plaintext passwords + my password
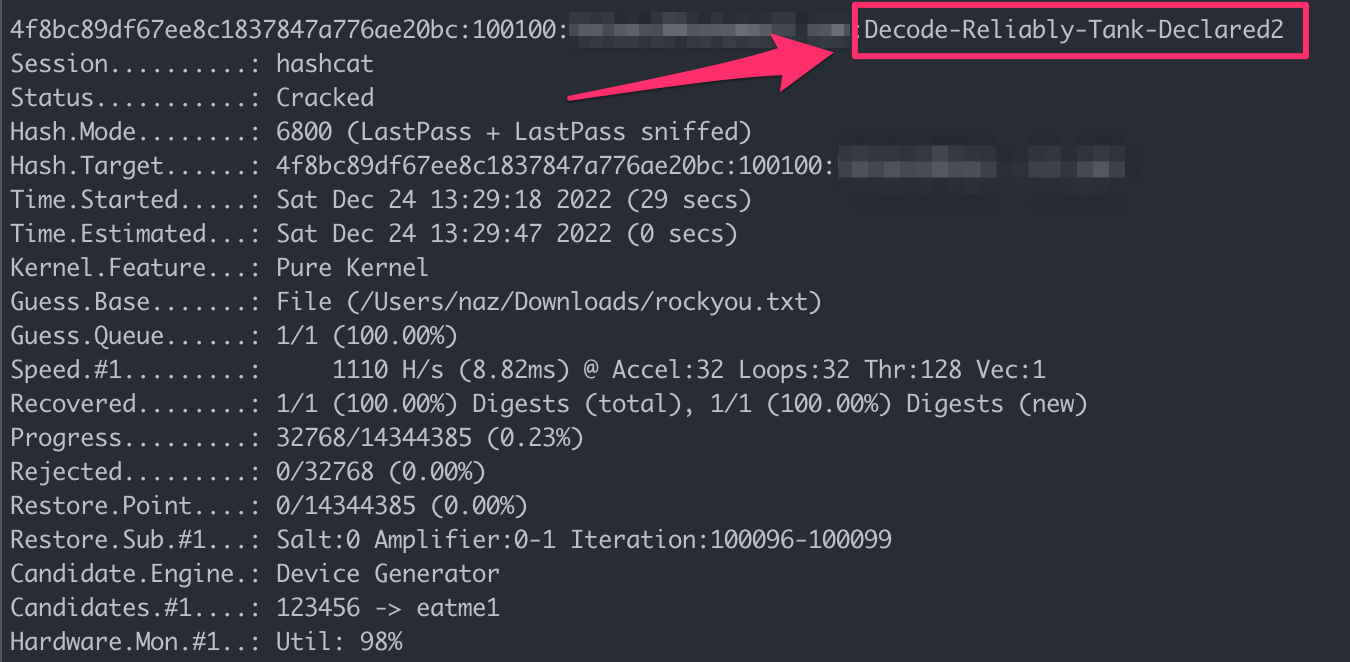
Note: This is only to demonstrate that the extracted values from above section do in fact correspond to the master vault password, you should ignore the time shown as it will take much longer than 29 seconds.
And there we have it, the master vault plaintext password successfully recovered.
